The Emergence of TrustBastion: A Troubling Threat
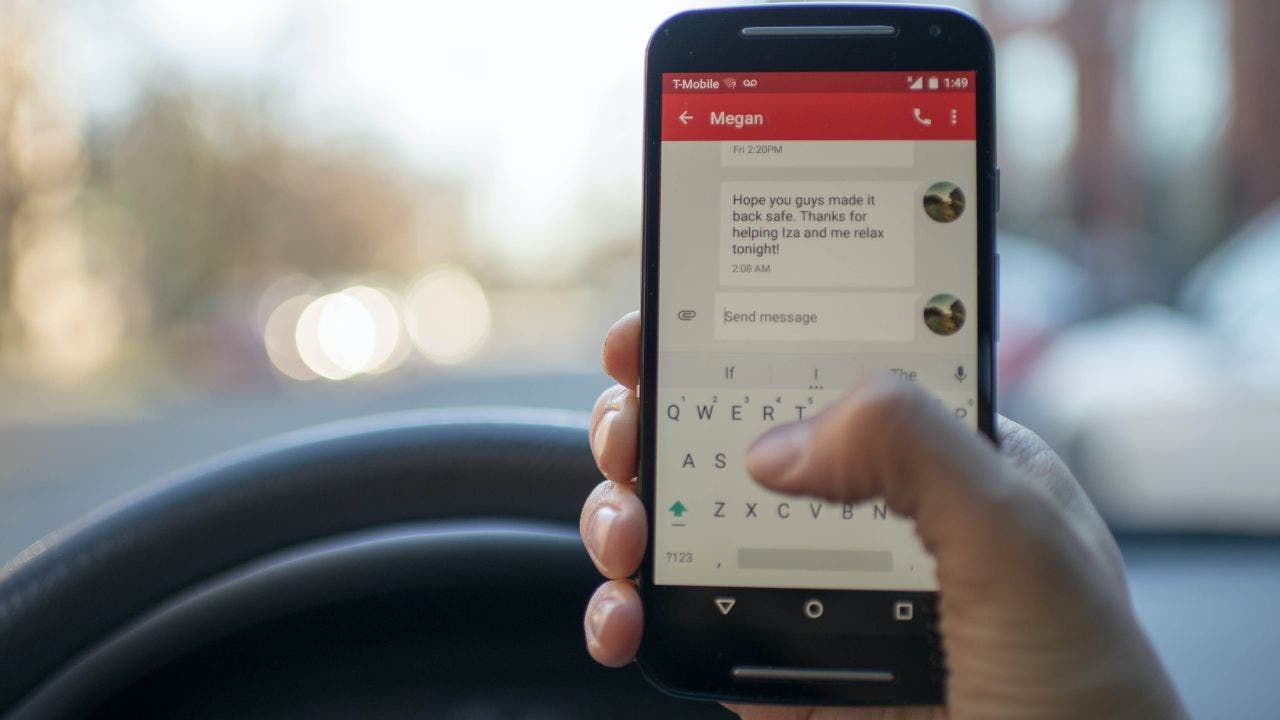
If you're an Android user, you need to be especially vigilant. Recent discoveries by cybersecurity experts reveal a deceptive application named TrustBastion that's posing as an antivirus solution. However, this unassuming facade is hiding a dark truth: it's a vehicle for sophisticated malware designed to infiltrate personal devices and pilfer sensitive information.
This alarming trend highlights not only the capabilities of bad actors but also the platforms they exploit. TrustBastion uses Hugging Face, a well-known repository for AI tools, to distribute its malicious code. This alarming combination of trusted tools and deceit underscores just how critical awareness and education are in today's digital landscape.
Understanding Hugging Face's Role
For those unfamiliar, Hugging Face provides an expansive open-source framework that has become a staple for AI researchers and developers. Within its user-friendly environment, innovative minds share natural language processing (NLP) models and machine learning algorithms. However, due to its openness, it has also become a hotbed for cybercriminal activity.
The accessibility of Hugging Face allows malicious entities to masquerade harmful content as legitimate files, hiding in plain sight among useful coding repositories. This profound shift in the use of trusted platforms reveals a new and concerning stage in the evolution of malware distribution.
The Mechanics of the TrustBastion Deception
The operational strategy behind TrustBastion employs well-tested psychological tactics aimed at reeling in unsuspecting users. Once downloaded, the app disingenuously claims that the user's device is infected, pushing them to install a so-called "update" that actually delivers the invasive malware. This method, coined “scareware,” exploits the fear and urgency that comes with potential infections.
The scenario presents a chilling reminder of the intersection of cybersecurity and human emotion. It serves as an urgent call to critically evaluate the applications we trust to safeguard our digital lives.
How the Malware Operates
According to reports from Bitdefender, this malware can:
- Capture screenshots of your device's activity
- Present fake login pages for financial applications
- Steal your lock screen PIN
These capabilities allow attackers to gain unprecedented access to individuals' financial and personal data. Once compromised, the stolen data can be transmitted to hackers, enabling them to initiate processes such as draining bank accounts or locking users out of their devices entirely.
The Aftermath: Google Weighs In
Google remains adamant that users can mitigate these risks by adhering to cautious behaviors. A spokesperson stated, “As long as users stick to official app stores, they're protected from this sort of malware.” This position emphasizes the importance of relying on validated platforms for app downloads, as Google's built-in protection mechanisms are designed to identify and neutralize known threats. However, this presumption can often lull users into a false sense of security.
Staying Vigilant: Protecting Yourself from Threats
As cybersecurity threats continue to evolve, it's imperative that users adopt proactive measures to safeguard their devices:
- Only download apps from reputable stores: By limiting downloads to official platforms like the Google Play Store, users lower their risk of encountering malicious software.
- Examine app reviews: Be suspicious of swaths of vague reviews or its sudden surges in ratings; they can signal ulterior motives.
- Utilize dedicated data removal services: Consider engaging services that monitor and protect your personal data. Reducing your digital footprint is a crucial defense against potential attacks.
- Run Play Protect: Regular device scans can identify and eliminate known threats.
- Avoid sideloading apps: Installing apps from outside the official repositories can introduce significant risks that users shouldn't overlook.
- Enable two-factor authentication: A strong and unique password, combined with two-step verification, significantly reduces the risk of unauthorized access.
Conclusion: A Cautionary Tale
This incident serves as a powerful reminder of the potential risks we face in an increasingly interconnected world. The environment where technological trust collides with malicious intent demands that we remain discerning and vigilant. As you navigate this digital landscape, always remain skeptical of the apps you trust. Cybersecurity isn't solely about avoiding sketchy applications—it's about questioning even the software that falsely claims to keep you safe.
Are you taking all necessary precautions to safeguard your personal devices? Let us know your thoughts and concerns at Cyberguy.com.
Key Facts
- Malicious App Name: TrustBastion
- Malware Distribution Platform: Hugging Face
- Main Functionality of Malware: Steal sensitive information
- Psychological Tactic Used: Scareware
- Example Capabilities: Capture screenshots, present fake login pages, steal lock screen PIN
- Recommendation by Google: Users should only download apps from official app stores
Background
A new Android malware threat called TrustBastion has emerged, disguising itself as an antivirus application while exploiting trusted platforms like Hugging Face to distribute malicious code. This incident highlights the evolving tactics of cybercriminals and the importance of user vigilance.
Quick Answers
- What is TrustBastion?
- TrustBastion is a malicious Android app that disguises itself as an antivirus solution to steal sensitive information from users.
- How does TrustBastion operate?
- TrustBastion uses scareware tactics to trick users into downloading updates that install invasive malware.
- What role does Hugging Face play in this malware?
- Hugging Face is used to host the TrustBastion malware within public datasets, allowing it to masquerade as legitimate software.
- What should users do to protect themselves?
- Users should only download apps from official stores, scrutinize app reviews, and enable two-factor authentication to improve security.
- What can the TrustBastion malware do?
- The malware can capture screenshots, show fake login pages for financial apps, and steal the user's lock screen PIN.
- What is the significance of scareware?
- Scareware exploits user fear and urgency, convincing them to install harmful updates under the pretense of fixing infections.
Frequently Asked Questions
What actions can protect me from TrustBastion?
Only download apps from reputable stores, run regular scans with Play Protect, and use strong antivirus software.
Is TrustBastion only targeting Android users?
Yes, TrustBastion specifically targets Android users by masquerading as a legitimate antivirus app.
Source reference: https://www.foxnews.com/tech/android-malware-hidden-fake-antivirus-app




Comments
Sign in to leave a comment
Sign InLoading comments...